As the world is trying to recover from COVID-19, vaccines have shown us how to prevent and control the spread of the COVID-19 pandemic. It is being established that access to the vaccine and rapid immunisation is crucial in achieving sustainable goals for businesses.
In the current operating climate, knowing how to plan for 'what's next' is crucial. To help guide this process BDO has drawn on its global team’s first-hand experience and insights to develop the 'Rethink' framework. Much of the world has moved past the react phase, and is heavily entrenched in resilience, where the goal is to identify what will help your organisation be success in the new normal.
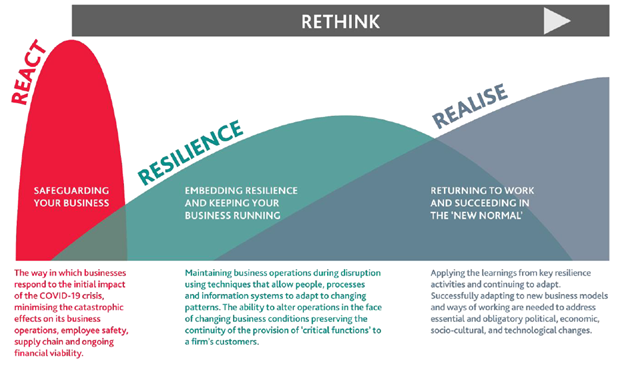
A "Rethought world" is where businesses successfully adapt to new business models and ways of working needed to address essential and obligatory political, economic, socio-cultural, technological and Cybersecurity changes.
As organisations survive through the 'Rethink' phases, i.e., 'React', 'Resilience' and 'Realise', and adopt new business models, Cybersecurity has emerged as one of the major areas which require significant attention for conducting the business securely and sustain. "Cybersecurity is the art of protecting networks, devices, and data from unauthorised access or criminal use and the practice of ensuring confidentiality, integrity, and availability of information." United States Cybersecurity and Infrastructure Security Agency (CISA)
Cybersecurity Trends
References:
Structural-Forces - Technology
3 Key Cybersecurity Trends to Know for 2021
These are the top cybersecurity challenges of 2021
The Top 8 Security and Risk Trends We’re Watching
Cybersecurity Professionals Stand Up to a Pandemic
Introduction to cyber security for Board members
2021 Top Ten Cybersecurity Trends
Subscribe to receive the latest BDO News and Insights
KEY CONTACTS
SHIVENDRA JHA
Head of Advisory and International Liaison Partner (ILP)
AMIT TENGLIKAR
Associate Director - Technology Advisory Services
Please fill out the following form to access the download.

